There are 2 sub-topics that I think need addressing:
- The unending crypto scams.
- What crypto actually IS.
These are two mutually exclusive topics. NEITHER defines the OTHER.
What are MY credentials to be able to speak about this?
I’m a software engineer with many decades of experience. I’ve been involved in cryptocurrencies since 2014. I have used many of the crypto services and many of the cryptocurrencies. I have traded dozens of cryptocurrencies and currently hold many cryptocurrencies. I have created my own blockchain from scratch and my own cryptocurrency completely from scratch with code. I’ve created neural networks and have trained them on price histories of cryptocurrencies to build price prediction AI. I understand the technology from top to bottom at a fundamental level and I understand the use of it and the tools and services built around it. I also understand the political thought processes involved in the creation of BitCoin as I hold similar, if not exactly identical beliefs as well.
Let’s talk about the scams first:
While crypto offers many benefits to humanity, scammers know that people are interested AND that people think they can get rich quick with crypto. They know it’s still relatively new and that most people are uneducated about it. They use those 2 facts AGAINST unsuspecting people and cheat them out of their money. This is a HUGE problem that NEEDS to be both addressed AND dealt with.
HOWEVER! The same is true for Gold, Stocks, US Currency, and anything else involving people’s hard earned income. This has absolutely NOTHING to do with “crypto”. Humans are a greedy species and that greed will and does manifest around everything. Crypto is no exception. The greed and scams are a fault of the greedy and the criminals, not a fault of the financial tools.
The PROBLEM is NOT the object of investment. The PROBLEM is the greed of the scammers (and to an extent, the greed of the victims, but that’s another story for another time).
Gold, Silver, precious metals, cash, and crypto are ALL vehicles of financial transactions and investments (well, cash is NOT an investment since it’s DESIGNED to devalue over time). Do NOT make the mistake of getting angry at the financial instrument simply because there are bad people out there taking advantage of people’s lack of education about them.
Let’s talk about CRYPTO in its own right:
I’ll precede this topic by stating that crypto exists to liberate you from the corrupt financial system controlled by tyrants and greedy and corrupt politicians. It WILL NOT liberate you from greedy, corrupt individuals that will do everything in their power to trick you out of your holdings.
Let’s examine whether or not it’s living up to that dream:
A basic primer on what cryptocurrencies ARE and then, what they are NOT
What Cryptocurrencies ARE:
There are many cryptocurrencies and not all are implemented with exactly the same backend technologies. My description will be as basic and non-technical as I can get away with while still providing you the facts you need to understand it. This will be a challenge (for me, not you), so bear with me. The REASON it’s a challenge is because I’m a highly technical person and have created my own crypto from scratch with code, so I understand that when I talk about things of this nature to non-technical people, I, like all technical people, have a language gap between me and you. I’ll do my best though:
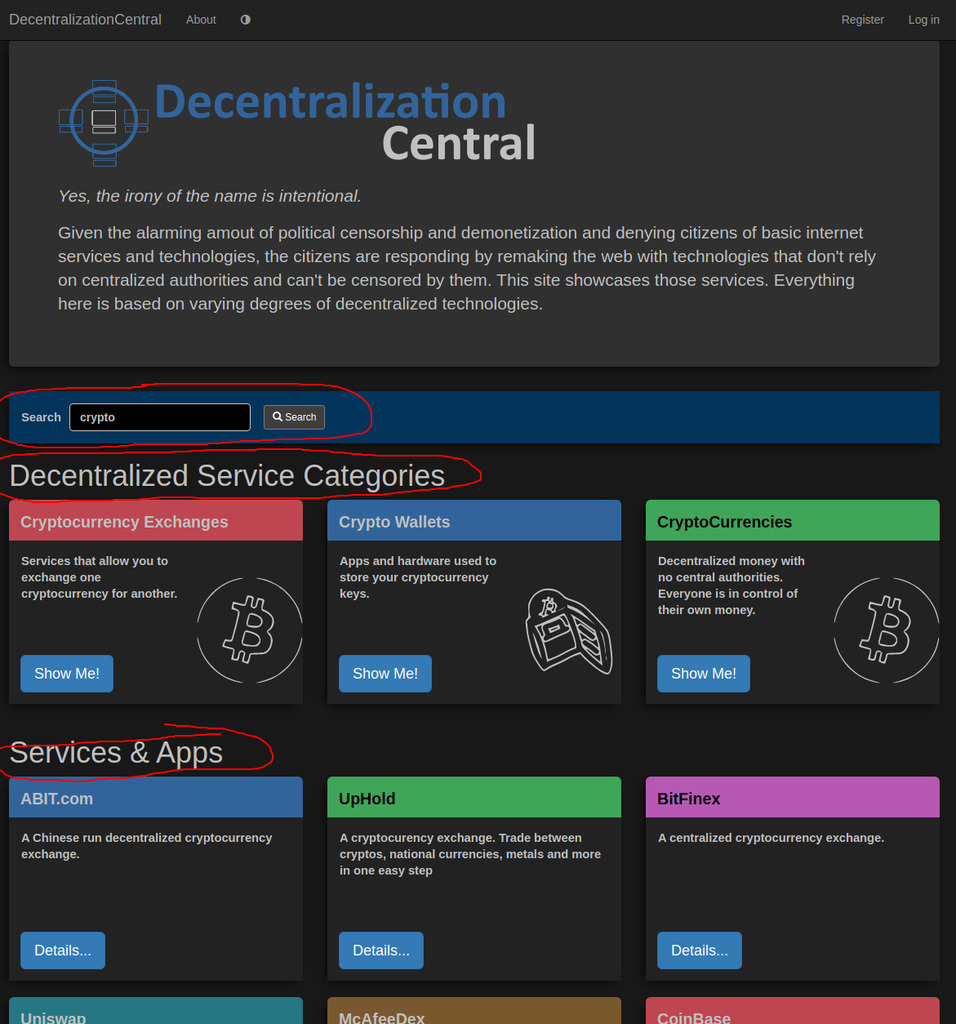
To understand crypto, we must first understand the system it’s designed to replace. It’s NOT designed to replace “money”. It’s designed to replace an entire corrupt and tyrannical financial system. This includes central banks, regular banks, credit cards, payment systems, all of which have denied services to people in recent years simply because of the individual’s political opinions. But THAT phenomenon has occurred SINCE the first cryptocurrency (#BitCoin) was invented. It was invented to protect your liberties from such tyranny, but at the time BitCoin was invented, we were in the middle of the 2008 housing collapse that destroyed the life savings of MILLIONS of Americans (and others around the world). One person, who to this day is still anonymous, decided enough was enough and designed a new currency that could NOT be controlled by a centralized authority. It was to provide the following functional differences from the current system:
- Impossible to forge the currency
- Impossible for your holdings to be confiscated by tyrants
- Impossible for your transactions to be blocked by tyrants
- Impossible for banks to hold or steal your money
- Impossible for central authorities to willy nilly devalue the currency by printing more
Notice that I did NOT mention “get rich quick”? That is not and was never a reason for cryptocurrencies.
How Things Are Going…
At the time of this writing, it’s September 2023. The BitCoin #whitepaper was released in January of 2009. It’s been 14 years. let’s examine each intended benefit and see how they’ve turned out so far.
1. Impossible to forge the currency
This has held up, at least for BitCoin and most cryptocurrencies. There have been thousands of cryptocurrencies created since the invention of BitCoin and some of those have been poorly designed and crypto was able to be forged. But not with the vast majority of them and most importantly, not with BitCoin. After 14 years and hundreds of thousands of white-hat hackers and actual bad guys trying to break it, it’s never happened.
Conclusion: SUCCESS!
For the remainder of this discussion, we’ll limit it to BitCoin since the nuances of the thousands of others are too many to cover. I may mention Ethereum, Monero, and stable coins, as those are notable and important to the discussion.
2. Impossible for holdings to be confiscated by tyrants
This too has held up. However, no doubt you’ve been blasted with stories of millions of dollars worth of crypto being confiscated by law enforcement or scammers or cryptocurrency exchanges going belly up. These are NOT cryptocurrency being confiscated by tyrants NOR BY ANYONE!
“WHY?” you ask?
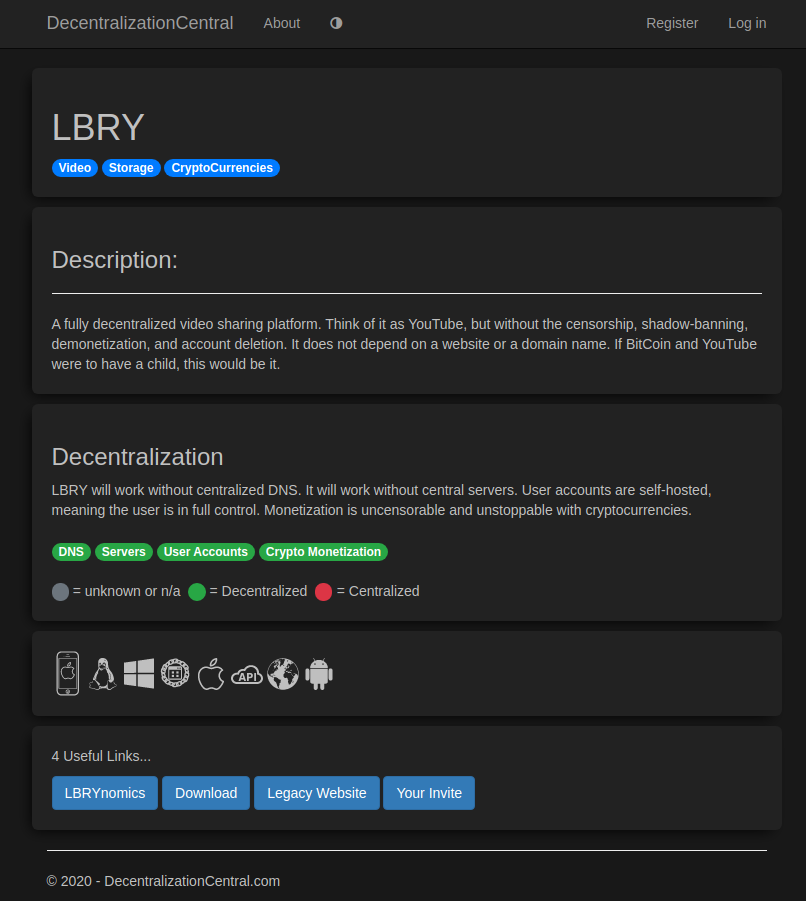
Great question! The confusion comes from the poorly written articles about these events and lack of understanding of what actually happened. Let’s discuss the first big event: Mt. Gox. This was the first cryptocurrency exchange. An exchange is bridge between the current legacy financial system and crypto. An exchange is where you go to exchange dollars for crypto and vice versa, as well as crypto for crypto.
AN EXCHANGE IS NOT CRYPTO! IT’S A CENTRALIZED AND PRIVATELY OWNED AND CONTROLLED BANK!
Mt. Gox was an exchange. It’s a centralized business… a bank. People would sign up with it, give their personal information, open an account, put fiat currency into it, and use the bank’s software (their website) exchange dollars for crypto and vice versa. All this did was update records in a database in the bank’s records. The customer didn’t actually own any crypto. They just had records in a centralized database that said that user could withdraw certain amounts of crypto. As long as they failed to withdraw the crypto they were entitled to into their own, personal wallet, it was never their crypto. It was the bank’s crypto. Many people didn’t understand that and many still don’t to this day. If you “have crypto” in an exchange, do do NOT have crypto. You have an IOU from the bank.
To actually “OWN” crypto, you MUST move it from the entity that holds it to your own, personal wallet where YOU possess the private cryptographic keys. Once you do that, THEN and ONLY THEN do YOU own the crypto. It’s that private key that makes you the owner. Your crypto absolutely, positively, MATHEMATICALLY CANNOT move without the use of that private key.
Mt. Gox got hacked.
Let me repeat that: —===>>> Mt. Gox got hacked <<<===
BitCoin DID NOT GET HACKED!
Mt. Gox was a centralized bank with bugs in their software. Hackers discovered the security flaws and used it to steal about a hundred million or so dollars worth of BitCoin FROM Mt. Gox! Why? Because they were able to control Mt. Gox’s software and instruct it to use Mt. Gox’s private keys to move the crypto.
This was a failure of Mt. Gox to protect their private keys. BitCoin functioned as it should have. The hackers did NOT break the encryption of BitCoin. They effectively stole the combination of the bank’s vault.
Not a SINGLE CUSTOMER’S BitCoin was stolen!
“But HOW can you say that? None of them have ever recovered their BitCoin to this day!”
Ah, but they NEVER POSSESED THE BITCOIN! It was NEVER THEIRS! Why? Because they never cashed in on their IOUs from the Mt Gox bank. Once Mt. Gox was drained of Mt Gox’s BitCoin, they lacked the BitCoin necessary to honor the IOUs that people’s fiat currency was given to them to purchase. This was a failure of a central bank. This central bank defeats the purpose of BitCoin.
YOU DON’T OWN BITCOIN IF IT’S IN A CENTRALIZED BANK! YOU OWN AN IOU!
in case it isn’t obvious at this point; If you purchase cryptocurrency from a centralized exchange, you must immediately move it to your own personal wallet were YOU control the keys. If you don’t do that, YOU SIMPLY DO NOT OWN ANY CRYPTO!
With the explanation of WHO actually owns BitCoin, let’s move on. We’re still examining the dream of “2. Impossible for holdings to be confiscated by tyrants”…
With the explanation above in mind, you’ve certainly heard of governments “confiscating crypto from people” by forcing a crypto exchange to hand it over to the tyrants. This is identical, technologically, to the Mt. Gox breach. It’s simply the government doing it rather than a hacker, but by force instead of a hack. Once again, they took resources in possession of a centralized bank. They did NOT hack the BitCoin blockchain nor did they control the BitCoin network to take it. The user’s simply did not own any BitCoin. The centralized bank did and they handed it over to the tyrants. If the user’s had already moved their claimed crypto into their own wallets, the tyrants would never have been able to take it.
Conclusion: SUCCESS!
The BitCoin blockchain has never been hacked. As long as you hold your private keys securely, your BitCoin can’t be taken.
3. Impossible for your transactions to be blocked by tyrants
No doubt you’ve heard about the Obama administration’s scheme called “Operation choke point”, where they unconstitutionally strong armed banks from doing business with gun stores? They intimidated banks into closing the accounts of 100% legitimate American businesses that sold firearms to American citizens for their constitutionally protected second amendment rights to bear arms.
You’ve also heard of Justin Trudeau’s Canadian government that locked the bank accounts of tens of thousands (might have been more) of Canadians because he disagreed with them for protesting. Not only did he lock THEIR accounts, but hey ALSO locked the accounts of individual citizens that were NOT protesting, but simply donated to the cause. In addition to THAT, he also ordered an American funding organization, GoFundMe, to hand over all donations that AMERICANS had made to the cause. Fortunately, GoFundMe refused.
These are just 2 well known examples, but this happens every day to various degrees.
You’ve probably heard of a story recently in the news of the U.S. government going after a decentralized cryptocurrency mixer called “Tornado”. It allowed users to send a chosen amount of crypto to the mixer, give it multiple other crypto wallet addresses and it would take the crypto received from multiple other people, mix it up, and then send it out to the wallet addresses (think of a wallet address as a bank account number) specified by the users. This allowed the users to then own their crypto anonymously to achieve privacy in their transactions. Of course, the government has the tyrannical belief that they should know about every single transaction that ever takes places throughout all of humanity. They are wrong, but that doesn’t stop them from claiming otherwise. They ordered centralized exchanges to not honor any crypto that touched any of those wallets.
Did this block transactions?
Yes and no.
Yes in that if anyone that owned those wallets wanted to move their crypto into the exchanges, they were blocked.
No, in that the blockchain and the network was not blocking it. It was individuals choosing to not accept transactions from wallets the government told them not to. The owners of that crypt are still, to this day, able to transfer it to any wallet they want and to accept crypto from any other wallet. The attempt by the government to black list those wallets was embarrassingly stupid in that all a user had to do was spend 10 seconds creating a new wallet and moving their crypto to the non-blacklisted wallet.
Conclusion: SUCCESS! (with noted exceptions of individuals choosing to follow orders)
4. Impossible for banks to hold or steal your money
At first glance, knowing that exchanges are banks and can hold and steal your crypto, you might think that with dream was a failure. In fact, it’s quite the opposite.
Simply don’t give your crypto to a centralized bank. Problem solved.
Of course, the centralized exchange banks are necessary as they are the on and off ramps to and from crypto and fiat. But, not entirely. Also, if you claim your IOU immediately by moving your just purchased crypto into your personal wallet, you’re then safe. You can also acquire crypto in many other ways. For example, you can run your own cryptocurrency mining software that generates crypto for you. You can sell products and services by accepting crypto directly from the buyer into your own, personal crypto wallet, bypassing the centralized banks.
If your crypt is in your own wallet where you and ONLY YOU have the keys, then it is, indeed, impossible for any bank to hold or steal your crypto because they simply don’t possess it. In crypto, YOU are LITERALLY your own bank.
Conclusion: SUCCESS!
5. Impossible for central authorities to willy nilly devalue the currency by printing more
This one is the one that seems to be most misunderstood by the general public. And it’s because the average person does not understand the technology that makes up cryptocurrencies. They CONSTANTLY argue against crypto saying, “Well, crypto is made from thin air. They can just make more at any time!”
This is fundamentally and completely FALSE! Here’s why:
(Prepare for techno-talk. I’ll keep it as limited as possible)
BitCoin comes into existence in only 1 way: Complex software algorithms are used to hunt for special numbers in a huge universe of numbers. Once a special number is found, the computer that found it presents it to the whole BitCoin network. The network validates the number is in fact a genuine special number and rewards the finder with a certain amount of Bitcoin. Any validator that lies is kicked out of the network and black-listed. Any computer claiming to have found a special number and isn’t validated by the network is also black listed. It’s financially harmful to be dishonest in that network.
The amount of computation and searching for one of those special numbers is ENORMOUS. The BitCoin network is the most powerful supercomputer on the planet; leaps and bounds more powerful than any government supercomputer. A BitCoin represents the enormous amount of computational time AND power consumed to generate it. There is no central authority that can authorize more BitCoin. The network only allows the creation of new BitCoins when a miner finds one of these numbers and on average, the entire global BitCoin mining decentralized network finds only ONE about every 10 minutes. At the time of this writing in 9/2023, this number is rewarded by the network with the creation of 6.25 new BitCoins. Every 4 years, the network cuts that reward in half. At the next 4 year cycle, it will be cut down to 3.125.
This is designed specifically to prevent deflation of the value of the cryptocurrency and is a direct result of the central banks choosing willy nilly to print TRILLIONS of new dollars, intentionally devaluing all existing dollars. The BitCoin network software is also designed to stop producing new BitCoins once 21 million BiCoins have been generated. As of right now, nearly 20 million have already been created. But with the halving event of every 4 years, it will take another 140 years to mine that last 1 million BitCoins.
THERE WILL NEVER BE MORE THAN 21 MILLION BITCOINS
Conclusion: OVERWHELMING SUCCESS!
FINAL CONCLUSION
Don’t hate a financial asset and tool just because there are bad people in the world. 100% of all financial assets and tools have always been, are now, and will always be tools used by scammers too. An asset is not defined by the bad guys. It’s defined by it’s function.
Don’t let your previous anger at the scammers cloud your judgement on BitCoin. In fact, it’s to the tyrants advantage that you let it cloud your judgement, because they WANT you to remain in the tyrannical financial system where they are gaining more and more control over everything you can do with your own money. They’re desperately hoping that light bulb of awareness never turns on in your head.
Cryptocurrency is the key to your financial liberties. Don’t deny yourself and your family your freedoms because of your misunderstanding caused by scammers and propagandists that want you to remain in the system that THEY control.