In this article in my series of “Encrypt All The Things!”, I’ll show you the specifics of encrypting a cloud drive using the Degoo.com cloud drive service. For a generic overview, that’s not Degoo specific, see:
If you use cloud drive services, of any kind, it’s critical that you do so ONLY with data that YOU have encrypted on YOUR END and that YOU are in control of the keys. Any service that handles the keys for you is NOT SECURE! The ONLY way your own data is secure is if YOU are in control of the keys. Some cloud drive services offer encryption at an extra price, which is crazy because you can do it FOR FREE with the added benefit of YOU being in control, NOT THEM!
The best way to ensure that you’re in control is for you to do the encryption yourself with software NOT provided by your cloud drive service.
In this article, I’ll show exactly how to do this with a commercial cloud drive service called Degoo.com and a free and open source encryption application called Cryptomator.
Create a Degoo account and install the software
First, you’ll need to sign up for the Degoo.com cloud drive service here.
Be sure to download and install the software. Don’t set up the download or sync folders yet. We need to get the encryption app installed first. BTW, Degoo has both free and paid options.
Install the Encryption App
Go to Cryptomator.org and download and install the software (It’s free and open source!). Once installed, you’ll need to setup one or more “vaults”, which are simply nothing more than a folder on your hard drive where encrypted files will be stored.

Set up a Cryptomator vault
First, you need to understand how Cryptomator works. DO NOT SKIP THIS!
The first time you run it, you will not have any vaults (encrypted folders). First, create a new folder on your drive in whatever way suits you best. This is where you’re going to have encrypted versions of your sync files stored.
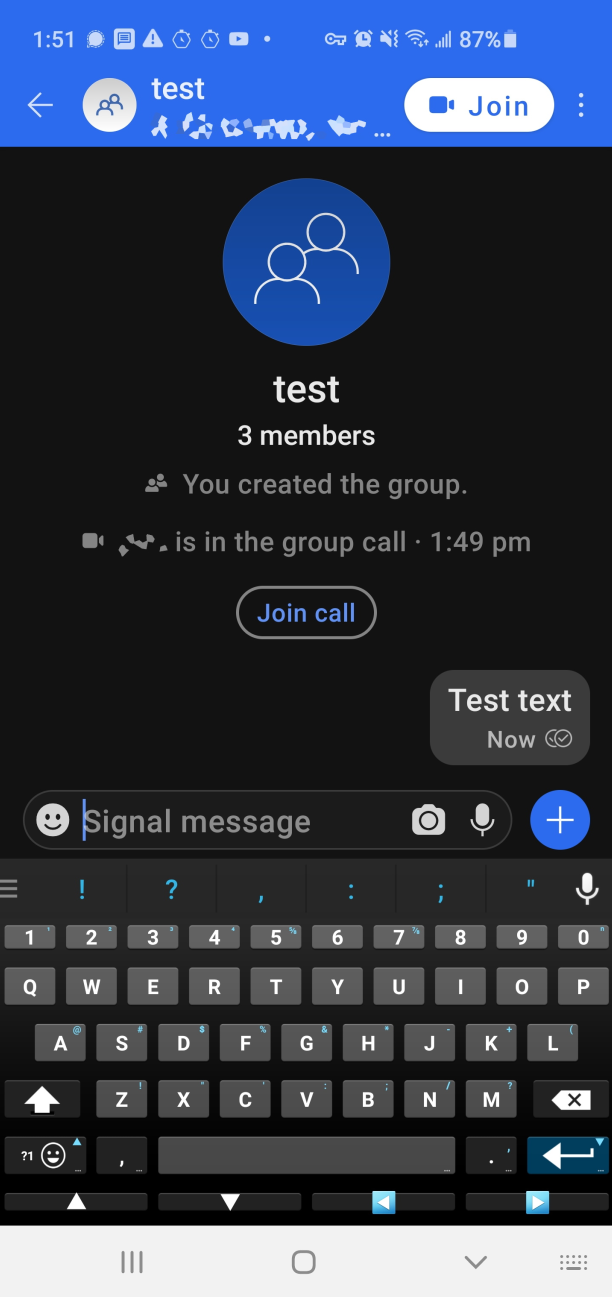
- Click the “+” sign in the lower left and choose “Create New Vault” to create a vault.

- Navigate to the folder you want to store your encrypted files (the folder should be blank, right now) and give it a name, here I Cryptomator.
- Then create a password for it. DO NOT FORGET THE PASSWORD OR YOUR DATA WILL BE LOST FOREVER!!!!!
- I Highly recommend saving it in a password manager like LastPass.com. I also recommend using that password manager’s password generator to generate a long, random password for you.
- Create the Vault by clicking the “Create Vault” button. This stores a couple of small files in there that cryptomator needs.
You’ll be prompted for the password again. This is not part of the vault creation process. You’re done. Now you’re ready to use it like you will everyday. Now you unlock the vault by entering your password.
- Click the “more options” button to see what you have available. Those options are pretty self-explanatory. I’ll skip those and let you choose how you want to configure it.
Your vault is now unlocked and is opened in a Windows Explorer window, usually as drive letter Z:.

The real folder on the real drive is here (below) (depending on where YOU chose to create it… this one is mine):

Now, I can store files in my Z: drive (as long as my vault is unlocked) and I can use any apps I want to read and write to the Z: drive. Everything works normally. Apps that read and write there have NO IDEA that they’re reading and writing to an encrypted folder.
You’ll notice that in Documents\deleteme\test (again, that’s where I created mine; yours will be where ever you put yours), you’ll see a “d” folder and 2 masterkey files. Those masterkey files have an ENCRYPTED version of your key. No one can decrypt it without knowing YOUR password that you just created. This masterkey file WILL BE ON THE REMOTE SERVER, so this is why you need a STRONG password, preferably random characters generated by a password manager.
As you save more files into your Z: drive, you’ll see more files show up somewhere under Documents\deleteme\test (again, MY folder is here, YOURS is where ever you put yours). The files that show up here have unreadable filenames and if you try to open them, they will have what appears to be garbage in them. These are the files you stored in your Z: drive, but these are encrypted.
Think of your Cryptomator unlocked vault Z: drive as a decrypted, magic window into your physical, encrypted files stored in their encrypted state in your Documents\deleteme\test (again, MY folder name I chose, YOURS will be different).
One caveate: Files in your Z-Drive CANNOT be larger than 2GB! That’s a limitation with the current version of Cryptomator.
I created a text file in my new Z: drive. As you can see below, Cryptomator created a file in the Documents\deleteme\test\d\WQ folder with a funky name. That’s what’s REALLY stored on my REAL hard drive. If I try to open the funky named file, it looks like garbage bytes. Both of those windows are showing the SAME data, it’s just that the REAL data is encrypted (top window). The bottom window is a VIRTUAL drive with an decrypted view of the data. ALWAYS remember this! You will NOT back up your Z drive! EVER! You’ll back up and/or sync your Documents\deleteme\test folder. More on that later.

Now, how to sync your encrypted files with Degoo.com
Now that you have a folder that contains your encrypted files and an easy way to use the the encrypted files (your cryptomator Z-drive), you need to sync the encrypted files to your Degoo.com account. DO NOT SYNC OR BACK UP YOUR Z: DRIVE!!!!!!
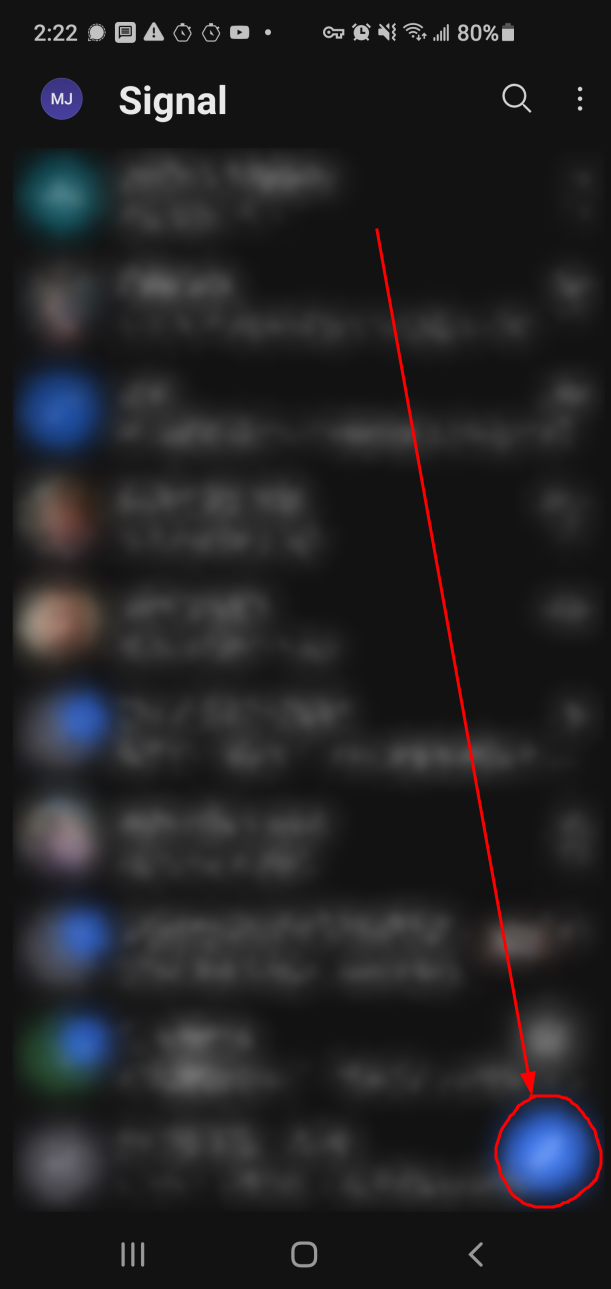
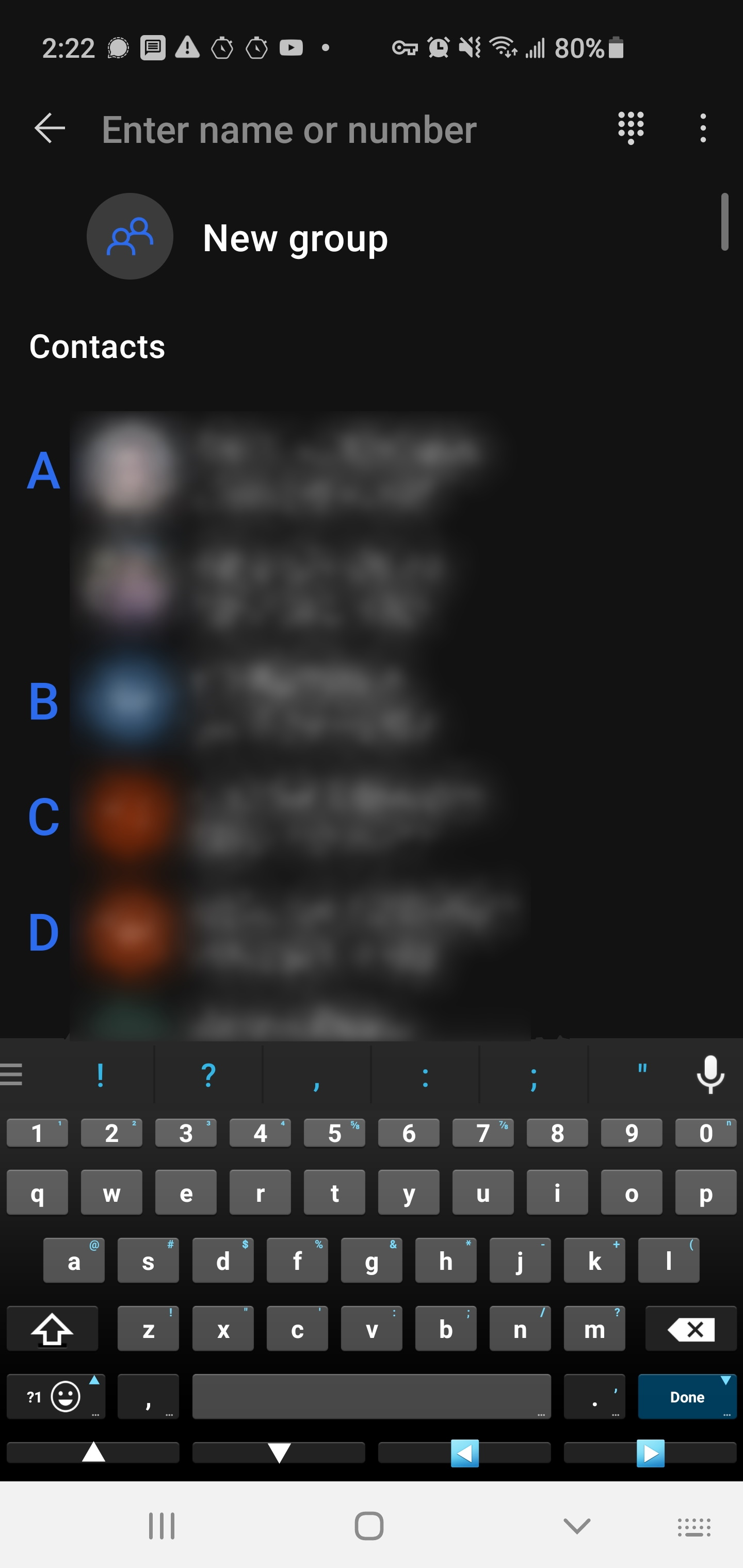
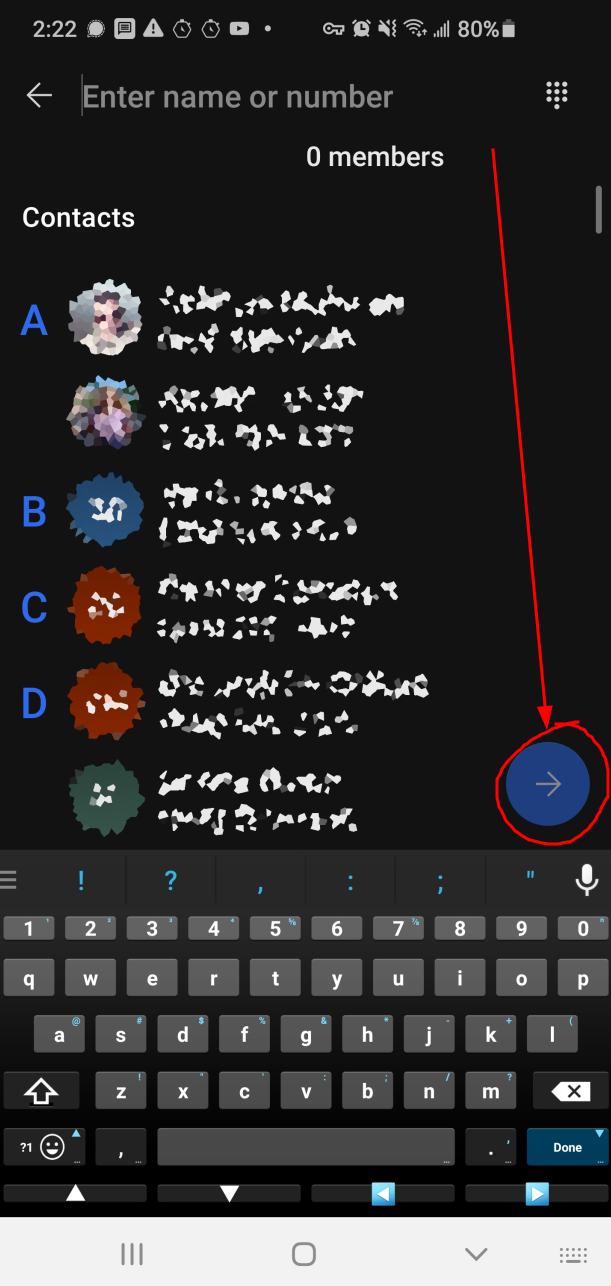
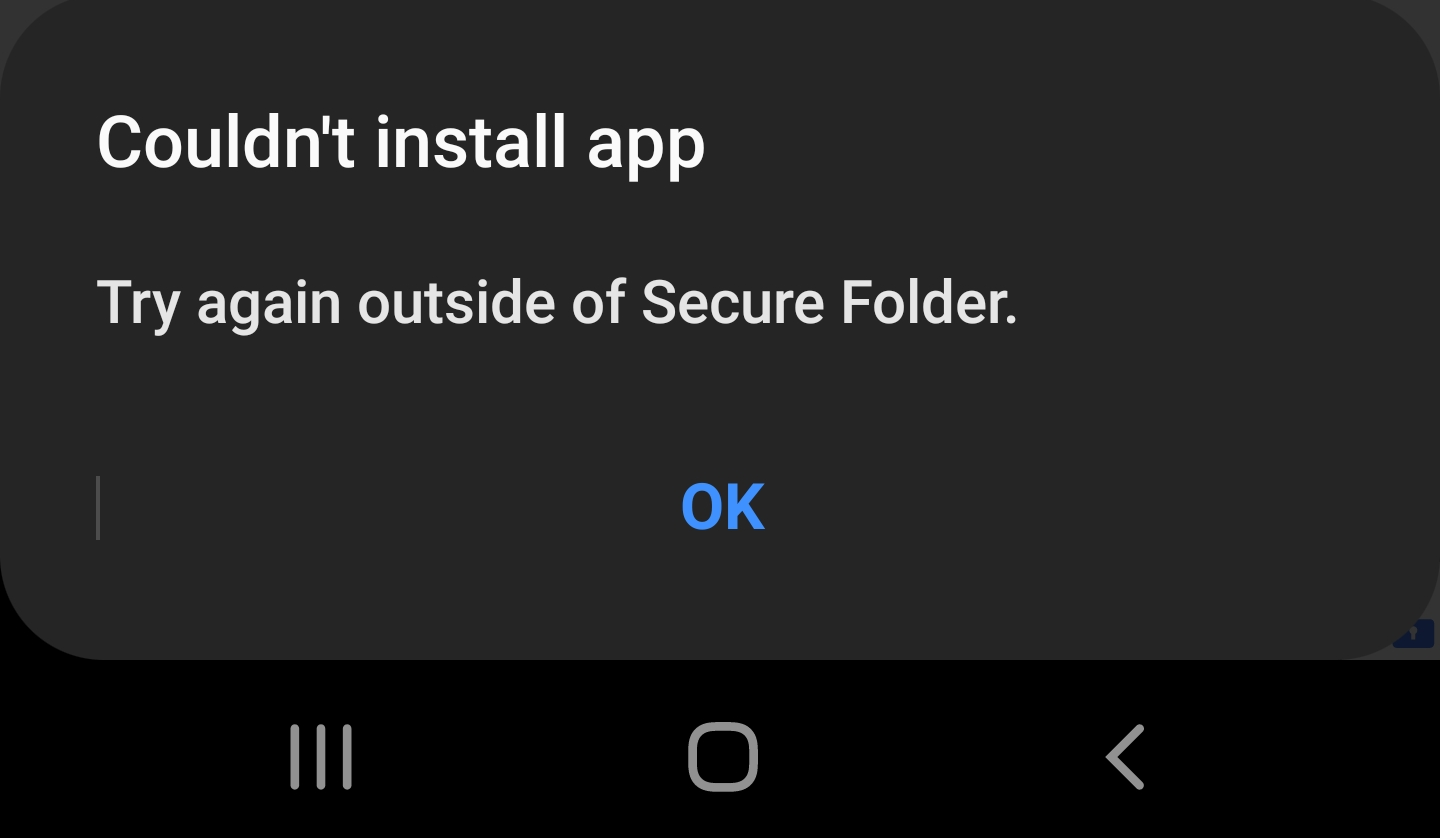
- If you haven’t already, download and install the software on Degoo.com and create an account.
- When you open it, click on the “Choose what to backup” tab. The actual folders on disk that are being backed up are each in their own cryptomator vault folder with encrypted files.
- Click the “Add folder to backup…” button and navigate to your Cryptomator vault folder… the one with the unreadable encrypted files NOT YOUR Z-DRIVE!!!! and click “Add folder to backup”
- Your folder will be added to your list of folders to be backed up.
Now, you’re all set. Anything you put into your Z-Drive is automatically encrypted at the time it’s written and since the real folder with the encrypted files is the one that’s backed up, you automatically get your data backed up in addition to automatically encrypted. Now, no matter how malicious anyone at Degoo may be (I have to reason to believe the are (or aren’t)), your privacy is safe. They cannot see anything other than what you see when looking at the encrypted version of your folder. Unless they have your password to your vault (which, of course, should be DIFFERENT from your Degoo password), they’ll never be able to see the contents.
But that was hard!
No it wasn’t! And, the small amount of work you did above is only done when creating a new vault and installing everything for the first time. Once it’s done, here’s all you need to do moving forward:
- Turn on your PC and log into Windows (or Mac or Linux)
- Start Cryptomator and unlock your vault.
That’s it! You can even shorten that to not have to start cryptomator setting up your vault to save your password and auto-unlock on start.
You can also add more cryptomator vaults at any time.
Quick review:
In this tutorial you did the following simple steps:
- Signed up with and installed Degoo.
- Downloaded and installed Cryptomator.
- Created a vault with Cryptomator.
- Told Degoo to sync the encrypted version of your cryptomator vault.
That’s really all you did. And now, you’re protected both with encryption and with an automatic, encrypted backup.
What’s Next?
Just continue to use your computer with your Z-Drive as your unencrypted version of your data. You can even lock your vault and Degoo will continue to back up your data. Degoo doesn’t need you to have it unlocked because it’s NOT backing up the unencrypted files. It’s only backing up the encrypted bits. Degoo isn’t even aware of the Cryptomator software. From Degoo’s software’s point of view, all that matters is that folder with the encrypted files in it.
Conversely, the Cryptomator software is unaware of Degoo. All Cryptomator knows is that you have a folder with encrypted files and it provides the means to unlock and use them.
You can create more vaults with Cryptomator, if you like and add them to Degoo as well.
You can create vaults inside your Google Drive sync folder, your Microsoft One-Drive sync folder, your DropBox sync folder, etc, etc… As many or as few as you want. Cryptomator works by encrypting any folder and providing an unencrypted view of it. Cloud drives work by backing up and/or syncing a folder. Put the two of them together and you’ve got a robust and secure backup strategy.
I do strongly recommend you make a cryptomator vault in EVERY cloud drive sync folder and move all your non-encrypted files INTO your virtual drive letter created for that vault.
WARNINGS!
You MUST obey the following rules!!!
- Don’t write files directly into your real folder that contains the encrypted files. If you do that, it will be backed up AS-IS… WITHOUT ENCRYPTION!
- Do NOT backup your Z: drive (or whatever drive letter cryptomator makes for you). That is DECRYTPED and if you back THAT up, you’ve wasted all your time and effort and are NOT storing an encrypted version of your files. Your Z: drive should ONLY be used for your normal work. DO NOT BACK IT UP!!!!
You are, of course, free to break these rules, but your secure backup is not going to be encrypted if you do break them.